CyberCriminals ? StayAwayFrom'Em ! Let'Em ComeToYou...
Translate
11/30/2013
Video: Our Safe Technology ? Radiating the People - Fukushima's Cancer Legacy
It's what POST-Fukushima Japan fears the most: Cancer. Amongst all accusations of government secrecy, worrying new claims, say a cancer cluster has developed around the Atomic Radiation Zone and that the most acclaimed victims are Children !
One man's little daughter is unaccounted for after the huge Tsunami destroyed the nearby town of Okuma, in Japan, on March 11th 2011. The Government stopped searching for her a long time ago. But, her father, Norio Kimura, has not and never will. At the same time, in a children's hospital, away from the forbidden zone, parents are hoping doctors won't find what they're looking for - Thyroid cancer.
Obamacare Weekend: It begins with a Website Shutdown
for Maintenance (Security?) Fixes
It was supposed to be D-Day for President Obama’s health care overhaul. But the government took down its website for a very long maintenance fix
A crucial weekend for the troubled Website that is the backbone of President Obama's healthcare overhaul appears to be off to a shaky start, as the government took the HealthCare.gov site offline for an unusually long maintenance period that lasted into Saturday morning.
Just hours before the Obama administration's self-imposed deadline to get the insurance shopping website working for the "vast majority" of its users by Saturday, the Centers for Medicare and Medicaid Services announced that it was taking down the website for an 11-hour period.
It was unclear whether the extended shutdown of the website - about seven hours longer than on typical day - represented a major setback to the Obama administration's high-stakes scramble to fix the portal, that it hopes eventually will enroll about 7 million uninsured and under-insured Americans under the Patient Protection and Affordable Care Act, also known as Obamacare.
At the very least, the shutdown suggested that nine weeks after the website's fatal launch on October 1st 2013 prevented most applicants from enrolling in coverage and ignited one of the biggest crises of Obama's administration, U.S. officials are nervous over whether Americans will see enough progress in the website to be satisfied.
For the administration and its Democratic allies, the stakes are enormous.
The healthcare overhaul is Obama's signature domestic achievement, a program designed to extend coverage to millions of Americans and reduce healthcare costs! (a verry good Thing !! G.D.) To work, the program must enroll millions of young, healthy consumers whose participation in the new insurance exchanges is key to keeping costs in check.
After weeks of around-the-clock upgrades of software and hardware, Obama officials said they were balanced to successfully double its capacity by this weekend, to be able to handle 50.000 insurance shoppers at the same time.
However, if the website does not work for the "vast majority" of visitors this weekend as the administration has promised, uninsured Americans from 36 states could face problems getting coverage by an initial Dec. 23 deadline.
It also could cause a stir that (could) extend to the 2014 elections when control of the U.S. House of Representatives (now controlled by Republicans) and the Senate (now led by Democrats) will be up for grabs.
Obama's fellow Democrats who are up for
re-election in Congress already have shown signs of taking distance from the president and his Healthcare program. If the website does not show significant improvement soon, some Democrats - particularly the dozen U.S. senators who are from states led by conservative Republicans and who are up for re-election next year - might call for extending Obamacare's final March 31 enrollment deadline for 2014.
That would delay the fines that are mandated by the law for those who do not have insurance by that date, a scenario that insurers say would destabilize the market. It also would fuel Republicans' arguments that Obamacare, and its website, are fatally flawed and should be scrapped.
Source: N.Y. Daily News
Related Posts:
11/29/2013
Kentucky Man will be sentenced March 2014 after trying to defraud Two Internet Companies per PayPal
A Fraudster from Covington, Kentucky, will be sentenced in March 2014 for defrauding two internet companies out of thousands of dollars (He faces a mandatory two year sentence on the aggravated identity theft count and maximum of 20 years on the wire fraud offense). One may wonder how a single man came through with a scheme of defrauding (2!) INTERNET Companies.
He (Melvin Dietz) pleaded guilty on November 19th this year that from January 2011 through December 2011, he arranged a scheme to defraud two online internet companies, WeBuyUsedCisco.com and Teksavers.com, both of which purchase used Cisco computers and equipment for Resell. The guy used 14 different PayPal accounts (each single one with a fake Identity for executing his scheme).
Now, shortly before or after he created an account, he contacted one of the companies and fraudulently offered to sell them certain Cisco items by pretending that he possessed them. Through e-mail, he used then one of his fake IDs, and bargained a price with a representative of one of those mentioned companies for the assumed Cisco equipment. At Dietz's instructions, the respective company transferred the payment for the equipment to one of the "fake" PayPal accounts that Dietz had set up using the same or a different alias identity every time. Right after, Dietz cut off communication and never sent the equipment.
To authorities, Dietz acknowledged he used or attempted to use the money in his PayPal accounts to purchase items online from other various online retail businesses or remove the money from his alias PayPal accounts in some other ways. The amount transferred by WeBuyUsedCisco.com & Teksavers.com to his PayPal account(s) totaled the amount of approximately 70.000 USD.
In committing his felony, Dietz knowingly used, without lawful authority, a means of identification of another person, during and/or in relation to the wire fraud count, in that he used that individual's Social Security number to obtain a prepaid Visa Card. Later Dietz used the card to validate the account with PayPal for the purpose of furthering his scheme to defraud Teksavers.com.
He (Melvin Dietz) pleaded guilty on November 19th this year that from January 2011 through December 2011, he arranged a scheme to defraud two online internet companies, WeBuyUsedCisco.com and Teksavers.com, both of which purchase used Cisco computers and equipment for Resell. The guy used 14 different PayPal accounts (each single one with a fake Identity for executing his scheme).
Now, shortly before or after he created an account, he contacted one of the companies and fraudulently offered to sell them certain Cisco items by pretending that he possessed them. Through e-mail, he used then one of his fake IDs, and bargained a price with a representative of one of those mentioned companies for the assumed Cisco equipment. At Dietz's instructions, the respective company transferred the payment for the equipment to one of the "fake" PayPal accounts that Dietz had set up using the same or a different alias identity every time. Right after, Dietz cut off communication and never sent the equipment.
To authorities, Dietz acknowledged he used or attempted to use the money in his PayPal accounts to purchase items online from other various online retail businesses or remove the money from his alias PayPal accounts in some other ways. The amount transferred by WeBuyUsedCisco.com & Teksavers.com to his PayPal account(s) totaled the amount of approximately 70.000 USD.
In committing his felony, Dietz knowingly used, without lawful authority, a means of identification of another person, during and/or in relation to the wire fraud count, in that he used that individual's Social Security number to obtain a prepaid Visa Card. Later Dietz used the card to validate the account with PayPal for the purpose of furthering his scheme to defraud Teksavers.com.
Two Singaporean arrested for Hacking Singapor's Presidential Website
Two Singaporean men have been arrested for allegedly defacing Singapor's president Tony Tan Website during a recent rash of Cyber Attacks in the city-state, police said on Thursday.
The men, aged 17 and 42, were arrested following a complaint lodged by the Website administrators of the Istana, the official residence of President Tony Tan.
The Website was hacked and displayed a crude image in the early hours of November 8, about an hour after Prime Minister Lee Hsien Loong's website displayed mocking messages and pictures from activist hackers' group Anonymous. Police said the two attacks are unrelated to each other.
The suspects in the Istana Website hacking will be charged in court on Friday, November 29th 2013, for offences under the city-state's Computer Misuse and Cybersecurity Act.
They face a maximum fine of Sg$10 000 or imprisonment of up to three years, or both.
Police did not reveal the identity of the two suspects, but Singaporean businessman Doolson Moo last week revealed to
The Straits Times newspaper, that he was the one who penetrated the Istana Website to “test for vulnerabilities”.
The 42-year-old said he entered a line of computer code into the search box on the website that allowed him to display a picture of an old woman pointing her middle finger, along with a string of offensive words in the southern Chinese dialect of Hokkien.
He told the newspaper that his accomplice was a 17-year-old student he knew through social networking site Facebook.
The arrests on Thursday came after another Singaporean, 35-year-old James Raj, was charged in court on November 12th 2013 with hacking a municipal council's Website and posting an image of a Guy Fawkes mask, the international symbol of Anonymous.
The council is located in a district represented by the prime minister.
A man claiming to speak for Anonymous has demanded that Singapore scrap a law requiring news websites to obtain annual licences.
The new Internet licensing rules came into force in June 2013 and have angered bloggers and activists who say they are designed to cover free expression.
Singapore strictly regulates the traditional media, but insists the new licensing rules do not have an impact on Internet freedom.
The men, aged 17 and 42, were arrested following a complaint lodged by the Website administrators of the Istana, the official residence of President Tony Tan.
 |
| Tony Tan |
The Website was hacked and displayed a crude image in the early hours of November 8, about an hour after Prime Minister Lee Hsien Loong's website displayed mocking messages and pictures from activist hackers' group Anonymous. Police said the two attacks are unrelated to each other.
 |
| Lee Hsien Loong |
They face a maximum fine of Sg$10 000 or imprisonment of up to three years, or both.
Police did not reveal the identity of the two suspects, but Singaporean businessman Doolson Moo last week revealed to
The Straits Times newspaper, that he was the one who penetrated the Istana Website to “test for vulnerabilities”.
The 42-year-old said he entered a line of computer code into the search box on the website that allowed him to display a picture of an old woman pointing her middle finger, along with a string of offensive words in the southern Chinese dialect of Hokkien.
He told the newspaper that his accomplice was a 17-year-old student he knew through social networking site Facebook.
| Guy Fawkes Mask |
The council is located in a district represented by the prime minister.
A man claiming to speak for Anonymous has demanded that Singapore scrap a law requiring news websites to obtain annual licences.
The new Internet licensing rules came into force in June 2013 and have angered bloggers and activists who say they are designed to cover free expression.
Singapore strictly regulates the traditional media, but insists the new licensing rules do not have an impact on Internet freedom.
Tips to Avoid Being Scammed the Next Holiday Season
In advance of the holiday season, its always good to beware of cyber criminals and their aggressive and creative ways to steal money and personal information. Scammers use many techniques to fool potential victims, including fraudulent auction sales, reshipping merchandise purchased with a stolen credit card, sale of fraudulent or stolen gift cards through auction sites at discounted prices, and phishing e-mails advertising brand name merchandise for bargain prices or e-mails promoting the sale of merchandise that ends up being a counterfeit product.
Internet criminals post classified ads or auctions for products they do not have. If you receive an auction product from a merchant or retail store rather than directly from the auction seller, the item may have been purchased with someone else’s stolen credit card number. Contact the merchant to verify the account used to pay for the item actually belongs to you.
Shoppers should be cautious and not provide credit card numbers, bank account numbers, or other financial information directly to the seller. Fraudulent sellers will use this information to purchase items for their scheme from the provided financial account. Always use a legitimate payment service to protect purchases.
Diligently check each seller’s rating and feedback along with their number of sales and the dates on which feedback was posted. Be wary of a seller with 100 percent positive feedback if they have a low total number of feedback postings and all feedback was posted around the same date and time.
The safest way to purchase gift cards is directly from the merchant or authorized retail merchant. If the merchant discovers the card you received from another source or auction was initially obtained fraudulently, the merchant will deactivate the gift card number and it will not be honored to make purchases.
- Fraudulent Classified Ads or Auction Sales
Internet criminals post classified ads or auctions for products they do not have. If you receive an auction product from a merchant or retail store rather than directly from the auction seller, the item may have been purchased with someone else’s stolen credit card number. Contact the merchant to verify the account used to pay for the item actually belongs to you.Shoppers should be cautious and not provide credit card numbers, bank account numbers, or other financial information directly to the seller. Fraudulent sellers will use this information to purchase items for their scheme from the provided financial account. Always use a legitimate payment service to protect purchases.
Diligently check each seller’s rating and feedback along with their number of sales and the dates on which feedback was posted. Be wary of a seller with 100 percent positive feedback if they have a low total number of feedback postings and all feedback was posted around the same date and time.
- Gift Card Scam
The safest way to purchase gift cards is directly from the merchant or authorized retail merchant. If the merchant discovers the card you received from another source or auction was initially obtained fraudulently, the merchant will deactivate the gift card number and it will not be honored to make purchases.
- Phishing and Social Networking
Be leery of e-mails or text messages you receive indicating a problem or question regarding your financial accounts. In this scam, you are directed to follow a link or call the number provided in the message to update your account or correct the problem. The link actually directs the individual to a fraudulent website or message that appears legitimate; however, any personal information you provide, such as account number and personal identification number (PIN), will be stolen.
Another scam involves victims receiving an e-mail message directing the recipient to a spoofed website. A spoofed website is a fake site or copy of a real website that is designed to mislead the recipient into providing personal information. (See Picture)
Consumers are encouraged to beware of bargain e-mails advertising one day only promotions for recognized brands or websites. Fraudsters often use the hot items of the season to lure bargain hunters into providing credit card information. The old adage:
"If it seems too good to be true, it probably is,"
is a good barometer to use to legitimize e-mails !
Black Friday has traditionally been the "biggest shopping day of the year." The Monday following Thanksgiving has more recently (2005) been labeled Cyber Monday, meaning the e-commerce industry endorses this special day to offer sales and promotions without interfering with the traditional way to shop. Scammers try to prey on Black Friday or Cyber Monday bargain hunters by advertising "one day only" promotions from recognized brands. Consumers should be on the watch for too good to be true e-mails from unrecognized websites.
Along with online shopping comes the growth of consumers using social networking sites and mobile phones to satisfy their shopping needs more easily. Again, consumers are encouraged to beware of e-mails, text messages, or postings that may lead to fraudulent sites offering bargains on brand name products.
Some tips you can use to avoid becoming a victim of Cyber Fraud this year:
- Do not respond to unsolicited (spam) e-mail.
- Do not click on links contained within an unsolicited e-mail.
- Be cautious of e-mails claiming to contain pictures in attached files, as the files may contain viruses. Only open attachments from known senders. Always run a virus scan on attachment before opening.
- Avoid filling out forms contained in e-mail messages that ask for personal information.
- Always compare the link in the e-mail to the web address link you are directed to and determine if they match.
- Log on directly to the official website for the business identified in the e-mail, instead of "linking" to it from an unsolicited e-mail. If the e-mail appears to be from your bank, credit card issuer, or other company you deal with frequently, your statements or official correspondence from the business will provide the proper contact information.
- Contact the actual business that supposedly sent the e-mail to verify that the e-mail is genuine.
- If you are requested to act quickly or there is an emergency, it may be a scam. Fraudsters create a sense of urgency to get you to act impulsively.
- If you receive a request for personal information from a business or financial institution, always look up the main contact information for the requesting company on an independent source (phone book, trusted Internet directory, legitimate billing statement, etc.) and use that contact information to verify the legitimacy of the request.
- Remember: If it looks too good to be true, it probably is.
Microsoft Releases Security Advisory for Microsoft Windows Kernel (2914486)
Microsoft has released Security Advisory 2914486 to address a vulnerability in a kernel component of Windows XP and Windows Server 2003. This vulnerability could allow an attacker to obtain elevation of privilege and then execute arbitrary code. Microsoft is aware of limited, targeted attacks that attempt to exploit this vulnerability in the wild.
http://technet.microsoft.com/en-us/security/advisory/2914486
TIMEOUT: Something to Relax...on Thanksgiving
Take 20 Minutes Timeout, take a look this Video (enlarged and if possible in HD), and Chillout. Happy Thanksgiving
11/28/2013
Cyber-Chat brings 77 Year Old Ex-WNEW DJ Dave Herman behind Bars for setting up a Sexual Rendezvous with a 7-year-old girl !
Dave Herman, 77, was arrested in October 24th, 2013 at the Henry E. Rohlsen Airport (Virgin Islands) after he tried to set up a sexual rendezvous with a 7-year-old girl, whose "mother" he chatted with, but was revealed to be an undercover investigator. Herman was extradited to New Jersey, where he appeared in federal court Wednesday to hear the charges against him. He could face a life sentence.
Former WNEW-FM morning host Dave Herman will wake up behind bars on Thanksgiving.
The 77-year-old DJ appeared Wednesday in Newark Federal Court, his eyes watery as he stood in a yellow prison jumpsuit one day after his return to New Jersey from the Virgin Islands.
Herman, other than recognizing his criminal behaviour nor the charges that he faces, said nothing during the courtroom appearance.
His attorney made no application for bail, although there was an understanding with prosecutors that the defense could return on short notice with a proposal.
But Herman, once a beloved radio personality, will spend the holiday in jail. No date was set for a reappearance in Court.
The Ex-DJ faces a possible life sentence if convicted of the charges. He was locked up in the Virgin Islands immediately after his arrest pending extradition to New Jersey.
He arrived back in the United States late Tuesday (11/26/2013), according to the U.S. Attorney's office in Newark.
Authorities, in a criminal complaint, charged that Herman pursued the child though cyber-chats with the "mother" for nearly a year before his arrest.
Screenshot:

Former WNEW-FM morning host Dave Herman will wake up behind bars on Thanksgiving.
The 77-year-old DJ appeared Wednesday in Newark Federal Court, his eyes watery as he stood in a yellow prison jumpsuit one day after his return to New Jersey from the Virgin Islands.
Herman, other than recognizing his criminal behaviour nor the charges that he faces, said nothing during the courtroom appearance.
His attorney made no application for bail, although there was an understanding with prosecutors that the defense could return on short notice with a proposal.
But Herman, once a beloved radio personality, will spend the holiday in jail. No date was set for a reappearance in Court.
The Ex-DJ faces a possible life sentence if convicted of the charges. He was locked up in the Virgin Islands immediately after his arrest pending extradition to New Jersey.
He arrived back in the United States late Tuesday (11/26/2013), according to the U.S. Attorney's office in Newark.
Authorities, in a criminal complaint, charged that Herman pursued the child though cyber-chats with the "mother" for nearly a year before his arrest.
"I find girls that age incredibly sexy, soft, and their innocence is also a huge turn-on for me," Herman allegedly wrote in one vile exchange. "Age 6 is the perfect time to start her being loved that way."
HOW SICK !!!
I guess the Radio Station should take away that Offer to buy 3 CDs for 50 bucks, featuring Hermans first show back in January 1997. Check This Link:
http://musicradio2005.ecrater.com/p/4748663/w-fm-dave-herman-1st-show
Screenshot:

Cyber Attack Across the Pacific Northwest: Electronic Payment Systems of Major Washington Grocery Stores Hacked !
Around 160 Wholesalers & Grocery Stores (URM Stores (mainly), Yoke's Fresh Markets & Rosauers Supermarkets) across the Pacific Northwest (Idaho, Oregon, Montana and Washington) are reported to be among those whose Electronic Payment Systems were hacked by Cybercriminals, whereby the affected Chain Stores are asking customers to pay with cash or check, after they have been "advised by Law Enforcement Officials and a Financial Institutions" that they may have been the target of a Cyber Attack against its payment processing system.
A third party computer security firm uncovered signs of an attack, and the company says it's cooperating with law enforcement and implementing additional security measures.
Some of their customers are discovering unjustified charges on their cards. From a Lake County Man in Montana, who found $75 in gasoline purchased in Texas, to Donald Frogner of Spokane, Washington, who was stunned to find he had paid for $18 worth of food at a Kentucky Fried Chicken in New Dehli, India.
Frogner said:
The common theme seems to be grocery stores that use URM Stores, a Spokane wholesaler, to process electronic payments, according to a Billings Gazette report. URM Stores, in turn, uses First Data Corp. of Atlanta to process its payment transactions. First Data has said it also is investigating the rash of card fraud occurring in Eastern Washington, western Montana and parts of Oregon. Computer Forensic experts also haven’t pinned down when the hack took place, or the method used. URM Stores has said it will continue to search for the source of the data breach that triggered a Sunday meeting with managers of the stores it serves.
It’s uncertain if the data breach occurred at the local store level or at some other point in the network, said URM Stores CEO Ray Sprinkle.
“Until these measures are in place, you should consider paying with cash or check,“ Ray Sprinkle
wrote in a statement (PDF).“Some stores may be able to process your card through a dial-up connection that is not affected by the attack. This process takes a few more minutes at the checkout stand and we ask for your patience.“
“This is a ridiculously horrible time for this to happen,” said Yoke’s CEO John Bole on Monday morning. As families stock up on groceries and beverages for Thanksgiving, “the timing almost couldn’t be worse for area grocers.“ he said.
Jeff Philipps, CEO of Rosauers, said the 21 stores in his group will offer 10 percent discounts on all purchases made on Monday. “We feel it’s fair because we didn’t tell people ahead of time they’d have to go through this.“ he said.
Spokane Media Federal Credit Union CEO Debie Keesee said that her institution is proactively replacing about 350 credit or debit cards, in order to protect those members from ongoing possible fraud.
On Monday, the company provided a toll-free number (001-877-237-7408) for customers who have questions about what has happened and want to know what steps they can take to protect themselves.
| URM Logo |
A third party computer security firm uncovered signs of an attack, and the company says it's cooperating with law enforcement and implementing additional security measures.
Some of their customers are discovering unjustified charges on their cards. From a Lake County Man in Montana, who found $75 in gasoline purchased in Texas, to Donald Frogner of Spokane, Washington, who was stunned to find he had paid for $18 worth of food at a Kentucky Fried Chicken in New Dehli, India.
Frogner said:
“This isn’t a bunch of teenagers hacking in and getting cards. This is a sophisticated effort,”in that some of the fraud involves using physical cards at some locations, instead of online fraud. He and his wife also saw more than $1.200 in unauthorized charges based in Florida State.
The common theme seems to be grocery stores that use URM Stores, a Spokane wholesaler, to process electronic payments, according to a Billings Gazette report. URM Stores, in turn, uses First Data Corp. of Atlanta to process its payment transactions. First Data has said it also is investigating the rash of card fraud occurring in Eastern Washington, western Montana and parts of Oregon. Computer Forensic experts also haven’t pinned down when the hack took place, or the method used. URM Stores has said it will continue to search for the source of the data breach that triggered a Sunday meeting with managers of the stores it serves.
It’s uncertain if the data breach occurred at the local store level or at some other point in the network, said URM Stores CEO Ray Sprinkle.
 |
| CEO Ray Sprinkle (left) |
“Until these measures are in place, you should consider paying with cash or check,“ Ray Sprinkle
wrote in a statement (PDF).“Some stores may be able to process your card through a dial-up connection that is not affected by the attack. This process takes a few more minutes at the checkout stand and we ask for your patience.“
“This is a ridiculously horrible time for this to happen,” said Yoke’s CEO John Bole on Monday morning. As families stock up on groceries and beverages for Thanksgiving, “the timing almost couldn’t be worse for area grocers.“ he said.
Jeff Philipps, CEO of Rosauers, said the 21 stores in his group will offer 10 percent discounts on all purchases made on Monday. “We feel it’s fair because we didn’t tell people ahead of time they’d have to go through this.“ he said.
Spokane Media Federal Credit Union CEO Debie Keesee said that her institution is proactively replacing about 350 credit or debit cards, in order to protect those members from ongoing possible fraud.
On Monday, the company provided a toll-free number (001-877-237-7408) for customers who have questions about what has happened and want to know what steps they can take to protect themselves.
A Secret Service investigation is under way !
Labels:
Credit Card Fraud,
Cybercrime,
First Data Corporation,
Grocery Stores,
Hacking,
Pacific Northwest,
Secret Service,
Spokane,
Supermarkets,
United States,
URM Stores
Video: The Internet Rising
Internet Rising is something inbetween Love Activity & a kind of streaming of webcam interviews, and its all conducted within the Webplanet. It is also a documentary about inspecting the emerging communication between the World Wide Web and the collective consciousness of humanity. Afterwards you might change a few points of view about the Internet (or about Life itself).
Hopefully !
The Internet Rising
You also can visit the Website of Internet Rising for other Videos, go to:
internetrising.net
See also: Internet Rising at IMDB
11/27/2013
November 26th 2013: One of the Longest Child Pornography Sentences in Colorado History goes to Richard Franklin
(a.k.a “westfaliaimplant”)
Denver Man Sentenced to 100 Years in Federal Prison for Advertising Child Pornography and Other Child Pornography-Related Crimes
 |
| Judge Wiley Y. Daniel |
Richard Franklin, a.k.a “westfaliaimplant”, age 45 of Denver, Colorado, was sentenced today by Senior U.S. District Court Judge Wiley Y. Daniel to serve 1200 months (100 years) in federal prison for:
- advertising child pornography,
- receipt of child pornography,
- two counts of distribution of child pornography,
- and possession of child pornography.
Franklin was indicted by a federal grand jury in Denver on June 8th, 2011. He was found guilty on August 27th 2013, following a seven-day jury trial. He was sentenced today, November 26th, 2013.
According to court documents, as well as facts presented at trial, from May 11th 2009 and January 5th 2011, Franklin knowingly made, printed or published any notice or advertisement offering to receive, exchange or distribute child pornography to anyone who was a member of his Online Trading Circle. Further, the defendant knowingly received and distributed child pornography using the Internet.
Lastly, Franklin knowingly possessed images of child pornography.
Lastly, Franklin knowingly possessed images of child pornography.
 |
| For example: Filesharing Software |
In total, the defendant possessed multiple hard drives containing over 200,000 images of child pornography. Franklin used a file trading software to allow others to preview and browse his collection and to chat with fellow child pornography traders. Part of the trading of images was to encourage purveyors to produce new child pornography videos. As a result of this investigation, two young children, both under 12 years old, were rescued from their abusers.When imposing the sentence, the Court stated that the crimes of the defendant were:
“pernicious and evil” and “must be dealt with in the most severe way.”
U.S. Attorney John Walsh said:
“The Department of Justice’s Project Safe Childhood continues to work aggressively to protect children from those who would exploit them. In cases such as this, we work diligently to punish those who provide these horrible images, with the goal of reducing both the availability and demand.”FBI Denver Special Agent in Charge Thomas Ravenelle said:
 |
| Thomas Ravenelle |
“The FBI will continue to aggressively pursue those who prey on children, especially those who advertise, trade and/or produce child pornography. Crimes of this nature threatened to destroy our most precious resource, offend every sensibility, and cannot be tolerated. The FBI and our partners will spare no expense or resource to bring them to justice.”
This case was investigate by the Denver and Phoenix Field Offices of the Federal Bureau of Investigation.
Additional Information about the Judge Wiley Y. Daniel can be found here.
IMPORTANT HOLIDAYS MESSAGE ! Cyber Fraud: Holiday Shopping Tips 2013
The Internet Crime Complaint Center (Also: IC3) gave out a communication today about Safe Shopping in front of the Holiday Christmas Season, especially about fraud online Shopping, so please be aware WHERE, FROM WHO & WHAT you want to buy ONLINE !
SOME IMPORTANT TIPS
Finally, check these additional sources to become even more informed on safe online shopping. Previous Holiday Shopping Tips public service announcements can be viewed on IC3.gov at the following links:
The FBI reminds holiday shoppers to beware of cyber criminals who are out to steal money and personal information. Scammers use many techniques to defraud consumers, from phishing e-mails offering too good to be true deals on brand-name merchandise to offering quick cash to victims who will re-ship packages to additional destinations. Previously reported scams are still being executed today.
While monitoring credit reports on an annual basis and reviewing account statements each month is always a good idea, consumers should keep a particularly watchful eye on their personal credit information at this time of year. Scrutinizing credit card bills for any fraudulent activity can help to minimize victims’ losses. Unrecognizable charges listed on a credit card statement are often the first time consumers realize their personally identifiable information has been stolen.
Bank transactions and correspondence from financial institutions should also be closely reviewed. Bank accounts can often serve as a target for criminals to initiate account takeovers or commit identity theft by creating new accounts in the victims’ name. Consumers should never click on a link embedded in an e-mail from their bank, but rather open a new webpage and manually enter the URL (web address), because phishing scams often start with phony e-mails that feature the bank’s name and logo.
When shopping online, make sure to use reputable sites. Often consumers are shown specials on the web, or even in e-mail offers, that look too good to be true. These sites are used to capture personally identifiable information, including credit card numbers, addresses and phone numbers to make fraudulent transactions. It’s best to shop on sites with which you are familiar and that have an established reputation as trusted online retailers, according to the MRC, a nonprofit that supports and promotes operational excellence for fraud, payments and risk professionals within eCommerce (LINK).
If you look for an item or company name through a search engine site, scrutinize the results listed before going to a website. Do not automatically click on the first result, even if it looks identical or similar to the desired result. Many fraudsters go to extreme lengths to have their own website appear ahead of a legitimate company on popular search engines. Their website may be a mirrored version of a popular website, but with a slightly different URL !!!
Purchases made on these sites could result in one or more of the following consequences:
- Never receiving the item.
- Having your credit card details stolen.
- Downloading malware/computer viruses to your CPU.
Here are some additional tips you can use to avoid becoming a victim of cyber fraud:
- Do not respond to unsolicited (spam) e-mail.
- Do not click on links contained within an unsolicited e-mail. (EXAMPLE)
- Be cautious of e-mail claiming to contain pictures in attached files; the files may contain viruses. Only open attachments from known senders. Scan the attachments for viruses if possible.
- Avoid filling out forms contained in e-mail messages that ask for personal information.
- Always compare the link in the e-mail to the link you are actually directed to and determine if they match and will lead you to a legitimate site.
- Log on directly to the official website for the business identified in the e-mail instead of “linking” to it from an unsolicited e-mail. If the e-mail appears to be from your bank, credit card issuer, or other company you deal with frequently, your statements or official correspondence from the business will provide the proper contact information.
- Contact the actual business that supposedly sent the e-mail to verify that the e-mail is genuine.
- If you are requested to act quickly or there is an emergency that requires your attention, it may be a scam. Fraudsters create a sense of urgency to get you to act quickly.
- Remember if it looks too good to be true, it probably is.
Finally, check these additional sources to become even more informed on safe online shopping. Previous Holiday Shopping Tips public service announcements can be viewed on IC3.gov at the following links:
- IC3 Announcement 2012
- IC3 Announcement 2011
- IC3 Announcement 2010
- US-CERT posted a Holiday Season Phishing Scams and Malware Campaigns release on November 19th, 2013, reminding consumers to stay aware of seasonal scams. The entire alert can be viewed here.
HAPPY HOLIDAYS & BE AWARE.
Season Greetings from here. :-)
Avoid These Holiday Online Scams
Latest News about John McAfee: John McAfee is like a persistent Computer Virus...
...this is how The Independent formulates it:
The news comes almost a year after Mr McAfee, 68, fled his previous home in Belize (see also: The John McAfee Story), in Central America, to escape being questioned by local police about the killing of his American neighbour, Gregory Faull.
The stalking complaint was filed by Connor Hyde, the superintendent of the building where Mr McAfee took an apartment earlier this year. Mr Hyde, a property manager for the Riverstone Residential Group, claims Mr McAfee sent him threatening emails and accused him of involvement in a conspiracy with Mr Faull’s family.
According to The Oregonian, Mr Hyde, who no longer works at the building in question, feared that Mr McAfee had access to firearms and associated with members of a biker gang.
In an interview with the Associated Press, Mr McAfee said he had not been evicted and insisted that he “never threatened anybody, except with threats of lawsuits”.
He had a “severe problem” with Mr Hyde due to “wilful lapses of security”, Mr McAfee said, adding that Mr Hyde “gave keys out to all of his friends and friends of friends… People were partying in vacant condos. It’s turned into a nightmare ever since the new owners purchased the building four months ago”.
A Portland judge granted a temporary protective order against Mr McAfee, who dismissed it as meaningless because, he said, he moved to Montreal in Canada two months ago. The tech guru also said he would not attend the hearing scheduled for January 3rd 2014.
Mr McAfee founded his anti-virus firm McAfee Associates in 1987 and sold his stake seven years later for an estimated $100m. The company was later sold to Intel for more than $7.6bn, while in 2009 its founder claimed to have lost the majority of his fortune during the financial crisis.
Four years ago, Mr McAfee moved to Belize for tax reasons, became an avid yoga practitioner and established a small biotechnology research facility where, he said, he was developing new varieties of antibiotics.
In April 2012, police raided the facility and arrested Mr McAfee on suspicion of producing methamphetamine, though the charges were quickly dropped.
On 11 November 2012, Mr Faull, a divorced sports bar owner from Florida, was found shot dead at his home nearby. He and Mr McAfee had reportedly argued about several matters, including the level of noise from Mr McAfee’s compound. The day before the murder, Mr McAfee’s dogs were poisoned.
Mr McAfee, who denies any involvement in Mr Faull’s death, dyed his hair as a disguise and fled Belize to avoid being questioned by the local authorities, whom he accused of corruption. While staying in neighbouring Guatemala, he met with a reporter and photographer from Vice Magazine who planned to chronicle his life on the lam.
But tragicly they gave away his location by posting a photo of Mr McAfee online without first wiping its location data.
Mr McAfee was accused of crossing the border from Belize illegally and spent a week in jail in Guatemala before flying (my expression fits better: fleeing) to the United States.
In a bid to clear his name, John McAfee has offered a $25,000 reward for information about Mr Faull’s death. Police in Belize said Mr McAfee remains a “person of interest” in their investigation into Mr Faull’s death.
The country’s Prime Minister, Dean Barrow, has described Mr McAfee as “extremely paranoid, even bonkers”.
Source: The Independent
"Like a persistent computer virus, wherever John McAfee pops up, trouble seems to follow."The British-American entrepreneur behind the McAfee anti-virus software has been evicted from his apartment in Portland, Oregon, and accused of stalking by the building’s property manager.
The news comes almost a year after Mr McAfee, 68, fled his previous home in Belize (see also: The John McAfee Story), in Central America, to escape being questioned by local police about the killing of his American neighbour, Gregory Faull.
The stalking complaint was filed by Connor Hyde, the superintendent of the building where Mr McAfee took an apartment earlier this year. Mr Hyde, a property manager for the Riverstone Residential Group, claims Mr McAfee sent him threatening emails and accused him of involvement in a conspiracy with Mr Faull’s family.
According to The Oregonian, Mr Hyde, who no longer works at the building in question, feared that Mr McAfee had access to firearms and associated with members of a biker gang.
In an interview with the Associated Press, Mr McAfee said he had not been evicted and insisted that he “never threatened anybody, except with threats of lawsuits”.
He had a “severe problem” with Mr Hyde due to “wilful lapses of security”, Mr McAfee said, adding that Mr Hyde “gave keys out to all of his friends and friends of friends… People were partying in vacant condos. It’s turned into a nightmare ever since the new owners purchased the building four months ago”.
A Portland judge granted a temporary protective order against Mr McAfee, who dismissed it as meaningless because, he said, he moved to Montreal in Canada two months ago. The tech guru also said he would not attend the hearing scheduled for January 3rd 2014.
Mr McAfee founded his anti-virus firm McAfee Associates in 1987 and sold his stake seven years later for an estimated $100m. The company was later sold to Intel for more than $7.6bn, while in 2009 its founder claimed to have lost the majority of his fortune during the financial crisis.
Four years ago, Mr McAfee moved to Belize for tax reasons, became an avid yoga practitioner and established a small biotechnology research facility where, he said, he was developing new varieties of antibiotics.
In April 2012, police raided the facility and arrested Mr McAfee on suspicion of producing methamphetamine, though the charges were quickly dropped.
 |
| Chrystal Meth... |
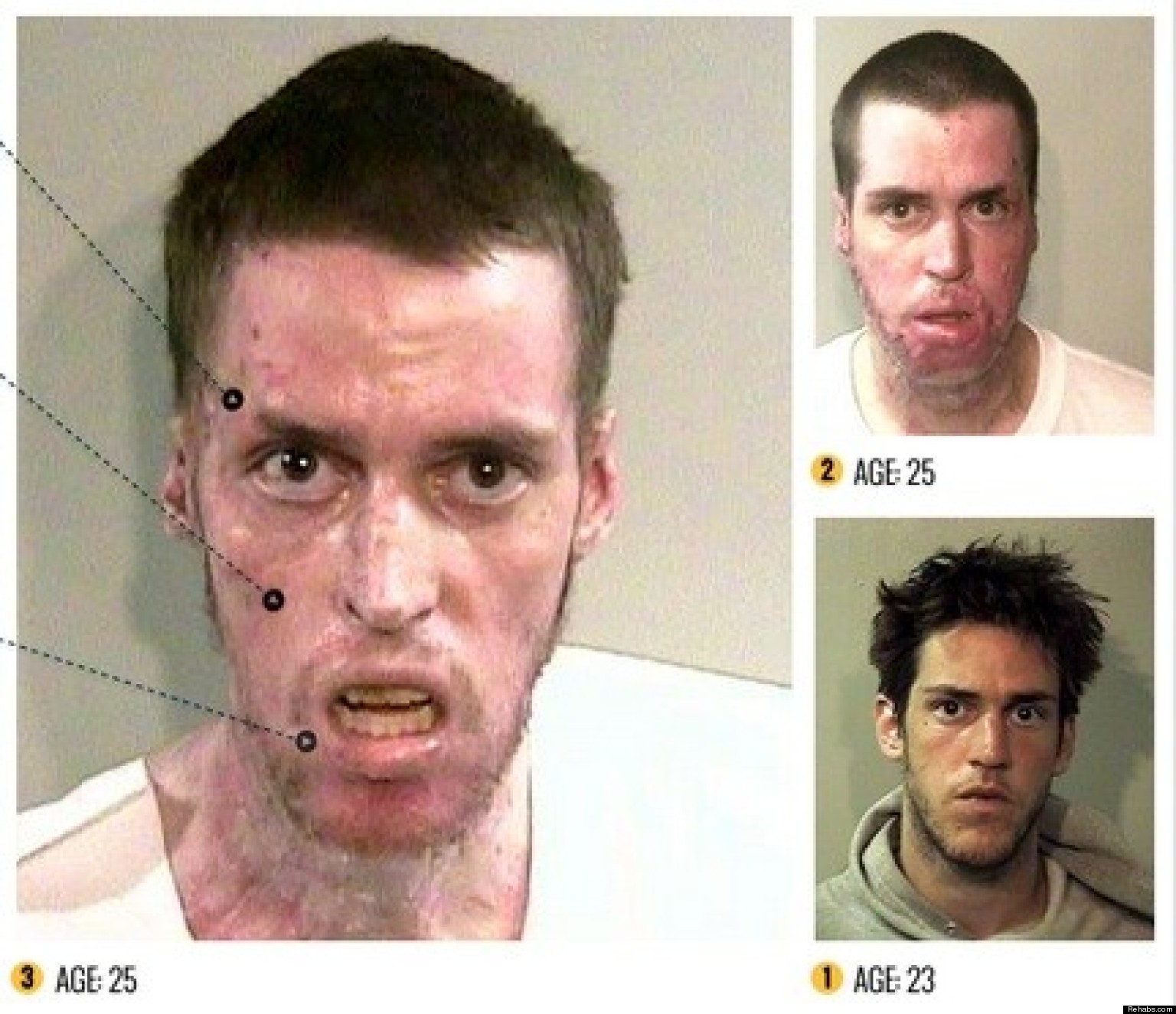 |
| ...and its optical Effects ! |
Mr McAfee, who denies any involvement in Mr Faull’s death, dyed his hair as a disguise and fled Belize to avoid being questioned by the local authorities, whom he accused of corruption. While staying in neighbouring Guatemala, he met with a reporter and photographer from Vice Magazine who planned to chronicle his life on the lam.
But tragicly they gave away his location by posting a photo of Mr McAfee online without first wiping its location data.
Mr McAfee was accused of crossing the border from Belize illegally and spent a week in jail in Guatemala before flying (my expression fits better: fleeing) to the United States.
In a bid to clear his name, John McAfee has offered a $25,000 reward for information about Mr Faull’s death. Police in Belize said Mr McAfee remains a “person of interest” in their investigation into Mr Faull’s death.
The country’s Prime Minister, Dean Barrow, has described Mr McAfee as “extremely paranoid, even bonkers”.
Source: The Independent
Is the Web full of Hate ? 101 East - Cyberbullying
This Video surrounds Cyberbullying. This Theme is seriously serious ! Think about it from above your own Websafety. Takes almost 25 Minutes !
In February 2012, Melbourne schoolgirl Catherine (Kat) Bernard took her life, after suffering depression and falling prey to Cyberbullying. Catherine Bernard is not the first, and wont be the last victim.
11/26/2013
Analysing Riskware II (Turbo Tool: RegCure Pro)
"It found 18906 problems which it fixed...."
RELATED POST: Part I
ANALYSING PROGRAM:
RegCure Pro
Screenshot:

ANALYSING PROGRAM:
RegCure Pro
THE FOLLOWING FILES/REGISTRY/KEYS RegCurePro IS WILLING (PROPOSES) TO DELETE, CALLING IT A SYSTEM PROBLEM, EVEN BETTER, CLASSIFYING IT AS A SECURITY RISK:
#5:
- AthCredentialProvider.dll
- MD5: 4b622ed5f0e940ef7d7778c351867fc6
- Publisher: Qualcomm Atheros
- Product: Bluetooth Software
- Description: Bluetooth Credential Provider
- File Location: C:\Windows\System32
RegKeyValue:
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\SharedDlls\C:\Windows\system32\AthCredentialProvider.dll
Screenshot:

Labels:
Boosting App,
Boosting Tool,
EEP64A.dll,
Fixing,
Key,
Microsoft Certified Partner,
OptPCEE3Prop.DLL,
R4EEP64A.dll,
RegCure Pro,
Registry,
Riskware,
RP3DHT64.dll,
RTEEP64A.dll,
Tuning App,
Tuning Tool,
Value
Symantec:
Blackshades Remote Access Tool (RAT) still being bargained
Cybercriminals are increasingly using the “Blackshades” Remote Access Tool (RAT), a malicious program whose source code was leaked three years ago, according to an analysis by Symantec.
Santiago Cortes, a security response engineer at Symantec, wrote in a blog post, that Blackshades, which Symantec identifies as “W32.Shadesrat”, has been infecting more MS Windows computers and is being controlled by many hundreds of CnC Botnets worldwide, despite the alleged arrest of Michael Hogue (a/k/a “xVisceral,”) in June 2012, the author who wrote the malicious code (program, tool).
As already mentioned, Blackshades is a Remote Access Tool (RAT) that collects usernames and passwords for email and/or Web services, Instant Messaging applications (like ICQ), FTP clients and many more. It has been sold on Black Hat Forums since at least 2010.
It’s common for hackers to use RAT’s, which can be used to upload other Malicious Software to a computer or to destroy and manipulate files. To avoid AV-Software, the program itself is often frequently modified, that is why a Malware Variant changes its name in the eyes of AV-Softwareanalytics, for instance this file is called W32.Shadesrat.C, usually means (like in this case), it’s the 3rd (A,B,C) modified (Variant) or, Generation, if you want so.
In his post, Cortes mentions that Lithuania and the United States have the highest number of command-and-control servers. Mostly all of those "Servers" have hosted exploit kits at some point in time, a type of baited trap that delivers additional malware to CPU’s with software vulnerabilities (don’t forget to update). Referring to Blackshades, Cortes says, that India, the U.S. and the U.K. have the most computers infected with this RAT.
Cortes writes:
Earlier this year, Symantec articled in a blog that a license to use Blackshades may cost around $40 to $100 a year.
To this graph, i’d like to point out to 2 earlier Posts of Malicious IPs , that likely shows how involved the small country Luxembourg, in the heart of Europe, is, inbetween Malicious Activity:
Symantec wrote as well that Blackshades had been promoted on underground forums by a person going by the nickname “xVisceral,”
In June 2012, the U.S. Attorney’s Office for the Southern District of New York announced the arrest of Michael Hogue (Rogue?) in Tucson, Arizona. Hogue was arrested with 23 others in a “carding” scheme, which involved trafficking in financial details.
FBI Article: Two-Year FBI Undercover “Carding” Operation Protected Over 400,000 Potential Cyber Crime Victims and Prevented Over $205 Million in Losses
He was charged with conspiracy to commit computer hacking and distribution of malware.
Santiago Cortes, a security response engineer at Symantec, wrote in a blog post, that Blackshades, which Symantec identifies as “W32.Shadesrat”, has been infecting more MS Windows computers and is being controlled by many hundreds of CnC Botnets worldwide, despite the alleged arrest of Michael Hogue (a/k/a “xVisceral,”) in June 2012, the author who wrote the malicious code (program, tool).
As already mentioned, Blackshades is a Remote Access Tool (RAT) that collects usernames and passwords for email and/or Web services, Instant Messaging applications (like ICQ), FTP clients and many more. It has been sold on Black Hat Forums since at least 2010.
It’s common for hackers to use RAT’s, which can be used to upload other Malicious Software to a computer or to destroy and manipulate files. To avoid AV-Software, the program itself is often frequently modified, that is why a Malware Variant changes its name in the eyes of AV-Softwareanalytics, for instance this file is called W32.Shadesrat.C, usually means (like in this case), it’s the 3rd (A,B,C) modified (Variant) or, Generation, if you want so.
In his post, Cortes mentions that Lithuania and the United States have the highest number of command-and-control servers. Mostly all of those "Servers" have hosted exploit kits at some point in time, a type of baited trap that delivers additional malware to CPU’s with software vulnerabilities (don’t forget to update). Referring to Blackshades, Cortes says, that India, the U.S. and the U.K. have the most computers infected with this RAT.
Cortes writes:
“The distribution of the threats suggests that the attackers attempted to infect as many computers as possible, the attackers do not seem to have targeted specific people or companies.”
Earlier this year, Symantec articled in a blog that a license to use Blackshades may cost around $40 to $100 a year.
To this graph, i’d like to point out to 2 earlier Posts of Malicious IPs , that likely shows how involved the small country Luxembourg, in the heart of Europe, is, inbetween Malicious Activity:
- IP 94.242.204.74 (From November 20th 2013)
- IP 80.92.67.155 (From November 24th 2013)
Symantec wrote as well that Blackshades had been promoted on underground forums by a person going by the nickname “xVisceral,”
In June 2012, the U.S. Attorney’s Office for the Southern District of New York announced the arrest of Michael Hogue (Rogue?) in Tucson, Arizona. Hogue was arrested with 23 others in a “carding” scheme, which involved trafficking in financial details.
He was charged with conspiracy to commit computer hacking and distribution of malware.
Labels:
Arizona,
Blackshades,
Botnet,
Cybercrime,
Exploit,
FBI,
Keylogger,
Lithuania,
Luxembourg,
Malware,
Michael Hogue,
RAT,
Remote Access Tool,
Santiago Cortes,
Spyware,
Symantec,
Tucson,
United States,
xVisceral
VIDEO: Cop Under Investigation After Concealed Carry Arrest
This unbelievable act took place a couple of years ago (June 2011) in Canton, Ohio
Canton police are investigating a verbal altercation between an officer and a driver who had a concealed carry permit for a gun.
Officer Daniel Harless was placed on administrative leave after the incident on June 8th 2011, according to Police Chief Dean McKimm.
By law in Ohio, drivers who are legally carrying guns, are supposed to tell officers immediately during a traffic stop if they have a gun in the car.
Twice after Officer Harless approached the driver's side of the car, William Bartlett speaks.
Once, he says "I got..." but doesn't finish his thought. The next time, he says, "before I get... I've never had to do this yet" but doesn't finish that thought as the officer asks for his drivers license.
About thirty seconds later, when he's out of the car, Bartlett says "I have a concealed carry."
"You have a gun on you?," Officer Harless asks.
A couple moments later, Harless becomes angry.
"You're supposed to tell me when you have a weapon," he screams.
"I was trying to,.." Bartlett replies.
"You're supposed to say that right off the [...] bat," Harless shouts.
Ohioans for a Concealed Carry say the officer was way out of line.
The advocacy group also says the state's law is a problem.
"The notification law fails everybody," says Philip Mulivor, a coordinator of the group.
Mulivor says Ohio should follow the lead of some other states and require officers to ask if there is a legal gun in the car, rather than requiring the driver to say it first.
Police Chief McKimm calls what he saw on the tape "totally unacceptable."
At one point, Officer Harless yells at Barlett, screaming "[....] talking to me with a [....] gun. You want me to pull mine and stick it in your head?"
"No sir, no sir," Bartlett replies.
Chief McKimm says the conduct on the video "violates standards we demand of our officers."
He says an internal investigation is underway after which a disciplinary hearing will be held.
Canton police are investigating a verbal altercation between an officer and a driver who had a concealed carry permit for a gun.
Officer Daniel Harless was placed on administrative leave after the incident on June 8th 2011, according to Police Chief Dean McKimm.
 |
| Dean McKimm |
By law in Ohio, drivers who are legally carrying guns, are supposed to tell officers immediately during a traffic stop if they have a gun in the car.
Twice after Officer Harless approached the driver's side of the car, William Bartlett speaks.
Once, he says "I got..." but doesn't finish his thought. The next time, he says, "before I get... I've never had to do this yet" but doesn't finish that thought as the officer asks for his drivers license.
About thirty seconds later, when he's out of the car, Bartlett says "I have a concealed carry."
"You have a gun on you?," Officer Harless asks.
A couple moments later, Harless becomes angry.
"You're supposed to tell me when you have a weapon," he screams.
"I was trying to,.." Bartlett replies.
"You're supposed to say that right off the [...] bat," Harless shouts.
Ohioans for a Concealed Carry say the officer was way out of line.
The advocacy group also says the state's law is a problem.
"The notification law fails everybody," says Philip Mulivor, a coordinator of the group.
Mulivor says Ohio should follow the lead of some other states and require officers to ask if there is a legal gun in the car, rather than requiring the driver to say it first.
Police Chief McKimm calls what he saw on the tape "totally unacceptable."
At one point, Officer Harless yells at Barlett, screaming "[....] talking to me with a [....] gun. You want me to pull mine and stick it in your head?"
"No sir, no sir," Bartlett replies.
Chief McKimm says the conduct on the video "violates standards we demand of our officers."
He says an internal investigation is underway after which a disciplinary hearing will be held.
From today on a historical Case: Missing Robert Levinson becomes the longest held hostage in U.S. history
Statement from Christine Levinson, wife of Robert (Bob) Levinson:
"Tomorrow, Tuesday, November 26, 2013, will mark an unimaginable milestone for my husband, Robert Levinson, who disappeared while visiting Kish Island, Iran, on March 9, 2007. On this day, Bob will become the longest-held American hostage, surpassing Terry Anderson who was held captive for 2,454 days.
No one would have predicted this terrible moment more than six and a half years ago when Bob disappeared. Our family will soon gather for our seventh Thanksgiving without Bob, and the pain will be almost impossible to bear. Yet, as we endure this terrible nightmare from which we can not wake, we know that we must bear it for Bob, the most extraordinary man we have ever known.
To whoever is holding Bob, I ask again for your mercy. Please let him go to reunite with his family.
Bob, if somehow you see or hear these words: Stay strong. You have a new grandson, just a month old. We can’t wait for you to meet him. We love you and will never stop working to bring you home safely."
FOR IMMEDIATE RELEASE November 25, 2013
CONTACT: WASHINGTON FIELD OFFICE (001) 202-278-3519
http://www.fbi.gov/washingtondc
Robert Levinson Becomes One of Longest Held Americans in History
Retired FBI Agent Went Missing on March 9, 2007WASHINGTON, D.C. — Tomorrow, November 26, 2013, Robert Levinson will become one of the longest held Americans in history, passing the 2,454 days Terry Anderson spent in captivity before being freed in 1991.
Mr. Levinson, 65, is a retired U.S. government employee with 28 years of service to the Federal Bureau of Investigation and the Drug Enforcement Administration. On March 8, 2007, Mr. Levinson traveled to Kish Island, Iran, as a private investigator; he went missing the following day.
The FBI is responsible for investigating crimes committed against U.S. citizens abroad and has been conducting an investigation to locate Mr. Levinson since 2007. In March 2011, the United States government announced it had received indications that Mr. Levinson was being held somewhere in southwest Asia.
“Exhaustive efforts have not yet been successful in locating Bob or establishing a dialogue with those who are holding him, but the FBI remains wholly committed to bringing him home safely to his loved ones,” said FBI Director James B. Comey. “We will continue to follow every lead into his disappearance, and we ask anyone with information regarding his disappearance to contact the FBI.”
On the fifth anniversary of his disappearance in March 2012, the FBI announced a reward of up to $1 million for information leading directly to the safe location and return of Mr. Levinson; that reward still remains unclaimed.
For more information regarding Mr. Levinson, to include reward information, please visit www.fbi.gov/levinson. Anyone with information regarding Mr. Levinson or his captors is asked to contact the FBI at https://tips.fbi.gov. Information will be kept confidential and can be provided anonymously.
Abonnieren
Posts (Atom)


































